“Linux is a Free Software that anyone can change. Is it possible for a threat actor to plant backdoor in Linux source code?“
My friend asked me this question and it is a good question. Since Linux is a Free Software that anyone can modify, it is reasonable to suspect that someone might changed it for malicious purpose. Has it happened before?
If you talk about someone planting a backdoor in the Linux Kernel source code, it hasn’t happened. This incident has occurred with other Free Software projects which makes up the Linux OS.
Linux Backdoor Attempts
AUR Backdoor
Recently in 16th July 2025, there was a backdoor disguised as a browser utility in Arch Linux User Repository (AUR).
Linux allows you to install many packages, from fonts to languages, from a compiler to IDE, even desktop environment or kernels that will heavily change your Linux. These packages are stored in repositories; think of repositories as an App Store but for Linux. Arch Linux has a repository for users submitted packages called AUR.
AUR allows any users to upload any kind of packages. A suspicious user, “danikpapas” uploaded three malicious packages, branded as “Browser Utilities Toolkit” but, it contains CHAOS RAT once installed. Arch Linux team has removed them on July 18, 2025, following community reports that flagged suspicious behavior from the packages.
XZ Backdoor
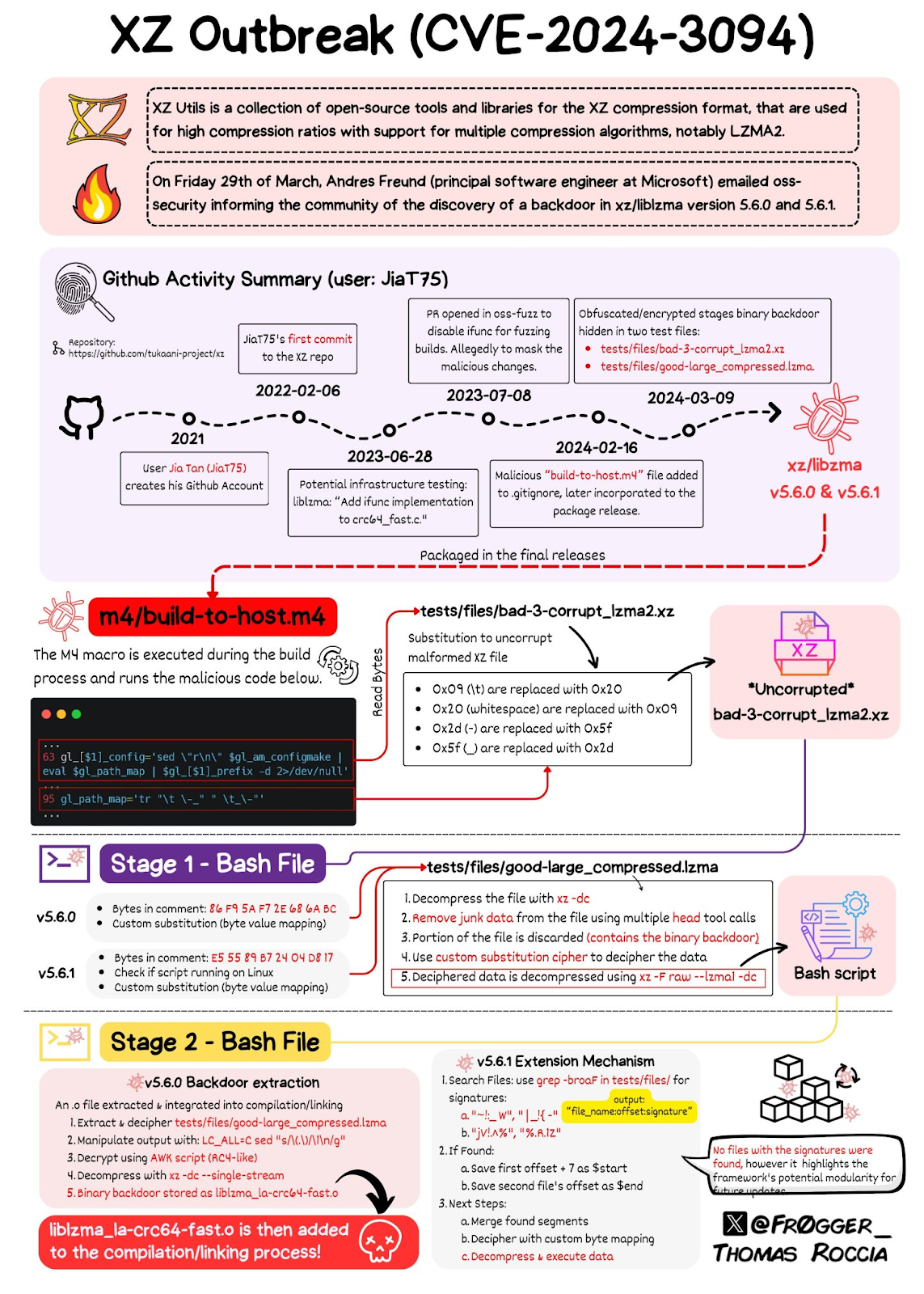
There was an even bigger case back in 2024, which shocked the entire world for the sophistication of the planned attack.
Andres Freund, a Postgre Developer, is doing usual task with his Linux machine. He noticed something is off; the program took so much resource which leads to ~500ms delay. A very short time for human yet, noticeably slow for a computer. Andres found the source of the problem, XZ, a legitimate Linux program.
“What’s the deal with XZ? Isn’t it just a Linux data compression utility?”, he thought to himself. Lasse Collin created XZ in 2005. It is a tool that compresses data into a file called .xz files, hence the name. The format is a popular way to compress Linux data and used by almost Linux distro.
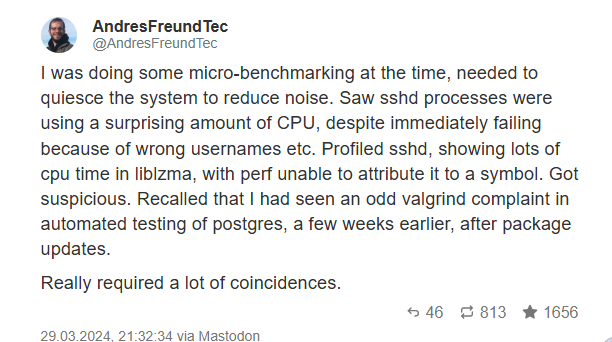
Andres reported the incident for further investigation. . American security researcher Dave Aitel suggested the link between Jia and SVR, a Russian intelligence service. Meanwhile, journalist Thomas Clauburn suggested the link with a non-state actor.
Since most Linux distro use XZ, the incident would be devastating so, Linux vendors responded quickly. Project Tukaani took down XZ version 5.6.0 and 5.6.1 . Redhat, Debian, and SUSE reverted the packages to an older version. Canonical postponed the release of Ubuntu 24.04.
Other Backdoor Attempts
Outside of Linux, programming languages are vulnerable to backdoor attempts too.
Python is widely used in Linux as an automation language with Bash, and AWK. Recently, security researchers found three packages with total 39,000 downloads. These three packages are in fact, malicious.
- disgrasya – 37,217 downloads
- bitcoinlibdbfix – 1,101 downloads
- bitcoinlib-dev – 735 downloads
In fact, these attempts are so common that there is an entire Github Repository dedicated to them. Security researchers called these attacks as supply chain attacks.
Conclusion
Linux is a Free Software which anyone can change so, someone can change it for malicious purpose too. You don’t need to worry however, since Linux vendors and communities constantly monitor these dangers. Whenever you want to install something, you need to be careful and make sure you trust the package. If you installed suspicious packages, follow the instructions to remove them.